Maya Tran
May 5, 2026
•
10 min

Most internal tools start the same way: someone hacks together a quick Retool app, points it at the production database, and ships it before lunch. It works. Then six months later you have twelve apps, no row-level security, a shared admin password, and an ops team that can accidentally delete customer records. The tool you built to save time is now the thing keeping you up at night.
This post is about avoiding that outcome. We'll walk through a production-grade architecture using Retool as the app layer and Supabase as the source of truth — covering how to enforce security at the right layer, design for multi-tenancy from day one, build audit trails that actually hold up, and decide when RetoolDB earns its place in the stack.
Retool is a UI builder. It's good at connecting inputs to queries and making things clickable. It is not a security boundary, a data governance layer, or a source of truth. The moment you treat it like one, you're building on sand.
Supabase gives you Postgres with a real access control model, a built-in auth system, edge functions, and an API layer that can enforce rules independently of whatever frontend is talking to it. That independence is the point. Your internal tool should not be the last line of defense between an ops employee and a customer's payment record.
The right mental model: Supabase owns the data and enforces who can touch it. Retool provides the interface. This means your security posture survives even if someone builds a second Retool app tomorrow, or a third tool using a different frontend entirely. The rules live in the database, not in the UI layer that someone will inevitably reconfigure.
In practice this means a few concrete things. First, connect Retool to Supabase through a dedicated service role or a Postgres role with minimum necessary privileges — not the postgres superuser. Second, enable Row Level Security on every table that contains tenant or user-scoped data before you write a single query in Retool. Third, treat the Supabase API URL and anon key as public by design; your real access control is RLS, not key secrecy.
If you skip this foundation, every security conversation you have later is just duct tape.
This is where most teams make a decision they regret. Retool has a permissions system — you can restrict which users can see which apps, which queries can run, and which components are visible. It's useful. It is not a substitute for database-level access control.
Here's the failure mode: you build a Retool app for your support team, lock it down with Retool's user groups, and feel secure. Then a developer queries the same table directly from Supabase Studio. Or someone exports a CSV from a second app that accidentally has broader scope. Retool permissions control what users can do inside a specific Retool app. Row Level Security controls what any connection to your database can do, regardless of where the query originates.
Use both — but understand what each layer is for.
Retool permissions are for UX and workflow control: hide admin actions from non-admin users, prevent accidental destructive operations, segment the interface by role. This is about experience and reducing surface area for mistakes.
RLS is for data integrity and security: ensure that a support agent can only read records for their assigned accounts, that a tenant's data is structurally isolated from other tenants, that even if a query is misconfigured it cannot return unauthorized rows.
A concrete RLS policy for a multi-tenant support tool looks like this: you add an account_id column to your tables, set a Postgres session variable at connection time with the current user's account context, and write a policy that checks account_id = current_setting('app.current_account_id')::uuid. Retool sets that variable via a pre-query before any data fetch. Even if the Retool query is wrong, the database policy holds.
The rule of thumb: if losing the Retool layer would expose data you don't want exposed, you don't have RLS right yet.
Multi-tenancy decisions made in month one are almost impossible to undo in month twelve. Get this right early.
There are three common patterns for multi-tenant data in Postgres. Row-level isolation, schema-level isolation, and database-level isolation. For most internal tools built on Supabase, row-level isolation is the right default. It's operationally simpler, plays well with RLS, and scales further than most internal tools need to go.
Row-level isolation means every tenant's data lives in the same tables, differentiated by a tenant_id or organization_id foreign key. RLS policies enforce the boundary. This works well when tenants are your customers and your ops team needs to work across all of them — you can write admin policies that bypass tenant-scoped RLS for specific roles while keeping the default behavior strict.
Schema-level isolation is worth considering if tenants have meaningfully different data shapes or you have hard compliance requirements that demand physical separation of data. The operational cost is real though — migrations have to run per-schema, tooling gets more complex, and Supabase's built-in features work against the public schema by default. Don't go this route unless you have a concrete reason.
Whichever pattern you choose, enforce these three things from the start:
tenant_id column, indexed, non-nullable, with a foreign key back to your tenants table. No exceptions. Adding this retroactively to a production table with 10 million rows is a painful migration.retool_admin Postgres role that has a BYPASSRLS attribute or explicit permissive policies. Audit who has that role. Don't just turn off RLS on a table because a query was inconvenient to write.In Retool, build your multi-tenant context into a shared resource configuration. Use a Retool environment variable or a resource-level header to pass the current user's tenant context on every request. If your support tool shows a dropdown to select which customer account to work on, that selected account ID should flow through every query via a consistent pattern — not hardcoded into 40 individual query strings.
One more thing: test your RLS policies before you go to production. Write a Postgres function that temporarily sets a session variable to a specific tenant and then runs a query. Verify that it cannot return rows from a different tenant. This takes twenty minutes and it will catch a misconfigured policy before your ops team finds it the hard way.
Audit logs are the thing everyone agrees they need and nobody designs properly until after an incident. Here's a concrete approach that works.
The goal is to answer three questions for any data change: what changed, who changed it, and when. A fourth question — why — is harder to capture automatically but can be added as a context field when the change is triggered from a Retool action.
Where to store it: a dedicated audit_log table in Supabase, separate from your operational tables. This table should be append-only. No deletes, no updates. Create a Postgres role for your audit log that only has INSERT privileges, and use that role for all audit writes. If a compromised connection can't delete audit records, your audit trail survives even a bad day.
Your audit log table schema should include at minimum:
id — UUID primary keytable_name — which table was affectedrecord_id — the primary key of the affected rowoperation — INSERT, UPDATE, or DELETEold_data — JSONB snapshot of the row before the changenew_data — JSONB snapshot of the row after the changechanged_by — the application user ID, not the Postgres rolechanged_at — timestamp with time zone, default now()context — JSONB field for app-level metadata like the Retool app name, action label, or a free-text reasonHow to capture it: Postgres triggers on your operational tables are the most reliable approach. Write a trigger function that fires AFTER INSERT OR UPDATE OR DELETE on any table you want to audit. The function reads OLD and NEW row data and inserts into your audit log. The key advantage of triggers is that they fire regardless of where the change originates — Retool, a migration script, a direct psql session, or a backend service.
The one gap with pure triggers is application-level context. A trigger doesn't know which Retool user clicked the button. Solve this the same way you handle RLS: set a session variable before the triggering query. In Retool, add a pre-query that runs SET LOCAL app.current_user_id = '{{ current_user.email }}'. Your trigger function reads that variable and stores it in changed_by. Now you have full traceability.
How to surface it: build a dedicated audit log viewer in Retool. A table component connected to a query on your audit_log table with filters for table name, record ID, date range, and user. For operational tables where an ops agent is viewing a specific customer record, add an inline audit history component that shows the last N changes to that specific record. This turns the audit log from a compliance checkbox into a tool your ops team actually uses to understand what happened.
Most internal tool projects treat staging as an afterthought. The production database is the real one, and staging is whatever someone stood up once to test something. This creates two specific failure modes: breaking changes get tested in production because staging doesn't reflect reality, and staging has real production data in it because someone copied a backup without thinking about it.
Neither of these is acceptable once your internal tools are touching anything sensitive.
The goal is two environments that are structurally identical but data-isolated. Same schema, same RLS policies, same Supabase edge functions, same Retool resource configurations pointing to different endpoints. Here's how to maintain this without making it a second job.
First, manage your Supabase schema through migrations, not through the Supabase Studio UI. Use a migration tool — Supabase CLI supports this natively. Every schema change, RLS policy, trigger, and function is a migration file committed to version control. Staging gets migrations applied before production. This is non-negotiable if you want environments to stay honest.
Second, set up Retool environments explicitly. Retool has a built-in environment concept — you can configure the same resource (your Supabase connection) with different credentials per environment. Your staging Retool apps point to the staging Supabase project, your production apps point to production. When you promote a change, the environment configuration follows. No manual credential swapping.
Third, deal with test data deliberately. Staging should have realistic but synthetic data — enough volume and variety to surface edge cases, but no real customer PII. Write a seed script that generates representative data for your domain. Run it once when you set up staging, run it again when you need to reset. If someone accidentally puts real data in staging, treat that as an incident, not a minor inconvenience.
Finally, automate the promotion path. Whether you're using GitHub Actions, Retool's deployment API, or a simple shell script — the process for moving from staging to production should be scripted, repeatable, and not require someone to manually copy SQL. The more manual your deployment process, the more likely environments drift apart.
RetoolDB is Retool's managed Postgres offering. It lives inside Retool's infrastructure and is purpose-built for internal tool data that doesn't belong anywhere else. There's a specific set of problems it solves well and a much larger set where you should use Supabase instead.
The case for RetoolDB as a sidecar — not a replacement for Supabase — is straightforward. Some data is genuinely Retool-specific: saved views, user preferences within an app, draft states for a multi-step workflow, feature flags scoped to internal tools, lightweight queues for ops task management. This data doesn't belong in your product database. It's tooling scaffolding. RetoolDB is a reasonable home for it.
The decision boundary is about ownership and portability. Ask: does this data need to exist if Retool disappeared tomorrow? If yes, it belongs in Supabase. If no — if it's purely about making your Retool apps work better — RetoolDB is a fine place to put it without adding complexity to your Supabase schema.
A practical example: you're building an ops workflow tool where agents process customer escalations. The escalation records live in Supabase — they're business data with audit requirements and multi-system dependencies. But the agent's personal saved filters, their in-progress draft notes before submitting a resolution, and the per-app notification preferences — those go in RetoolDB. Clean separation, no pollution of your source of truth.
Where RetoolDB doesn't make sense: as a caching layer for Supabase queries, as a place to store data you're scared to put in Supabase, or as a workaround for RLS policies you haven't figured out yet. If you're reaching for RetoolDB to avoid doing database design properly, that's a signal to stop and fix the design.
One operational note: RetoolDB doesn't have the same RLS capabilities as Supabase Postgres. It's a simpler offering. Don't try to enforce multi-tenant data isolation there — it's not the right tool for that job. Keep sensitive, tenant-scoped data in Supabase where you have full policy control.
The right Retool + Supabase architecture isn't complicated once you've internalized the principle: every layer should do what it's actually good at. Supabase owns the data and the rules. Retool owns the interface and the workflow. RetoolDB handles the tooling scaffolding that doesn't belong anywhere else. Build with that division of responsibility from day one and you'll have an internal tool stack that's still sane when you're running twelve apps and onboarding your fourth ops team member.
Looking to supercharge your operations? We’re masters in Retool and experts at building internal tools, dashboards, admin panels, and portals that scale with your business. Let’s turn your ideas into powerful tools that drive real impact.
Curious how we’ve done it for others? Explore our Use Cases to see real-world examples, or check out Our Work to discover how we’ve helped teams like yours streamline operations and unlock growth.
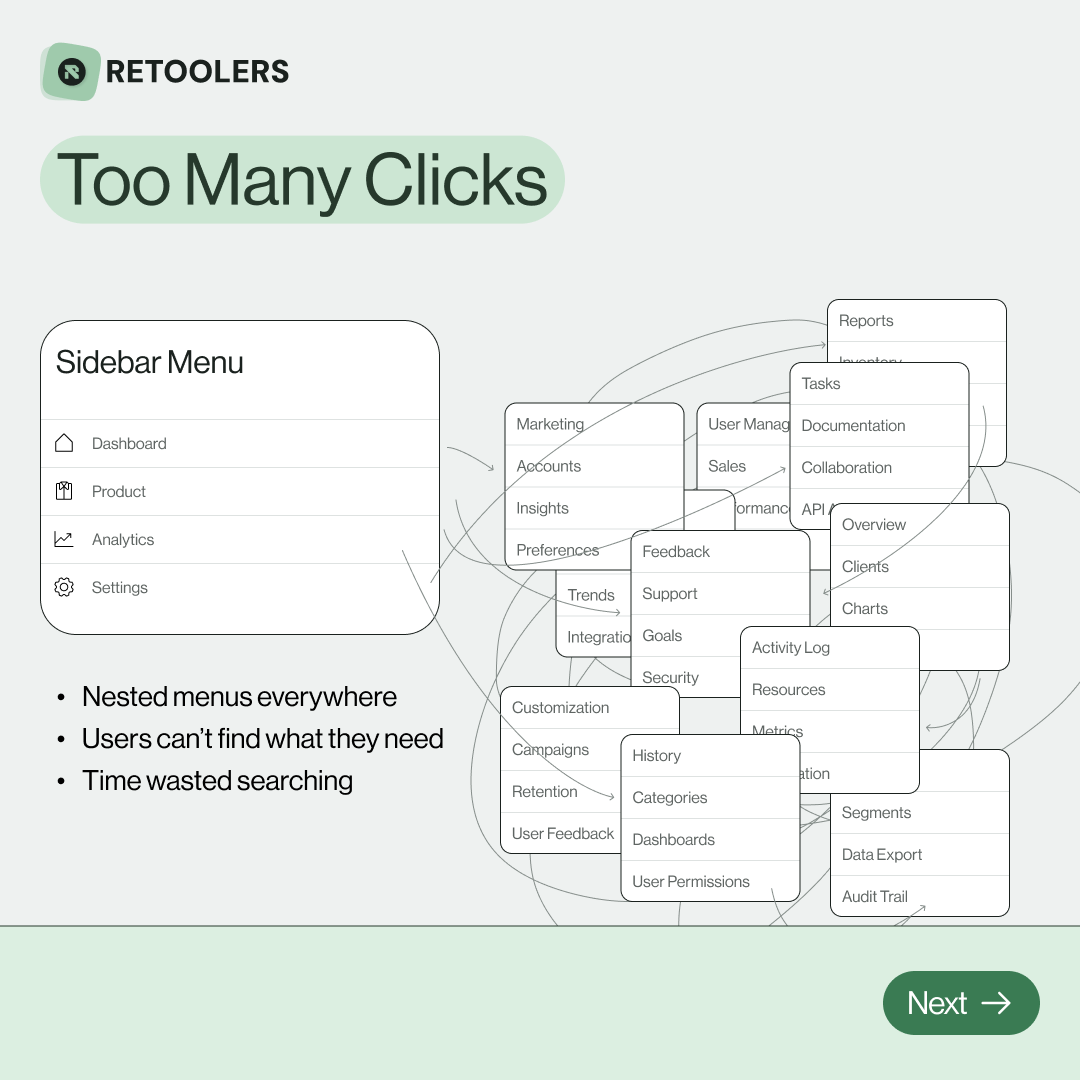
🔎 Internal tools often fail because of one simple thing: Navigation.
Too many clicks, buried menus, lost users.
We broke it down in this 4-slide carousel:
1️⃣ The problem (too many clicks)
2️⃣ The fix (clear navigation structure)
3️⃣ The Retool advantage (drag-and-drop layouts)
4️⃣ The impact (happier teams)
💡 With Retool, you can design internal tools that are easy to use, fast to build, and simple to maintain.
👉 Swipe through the carousel and see how better UX = better productivity.
📞 Ready to streamline your tools? Book a call with us at Retoolers.

🚀From idea → app in minutesBuilding internal tools used to take weeks.
Now, with AI App Generation in Retool, you can describe what you want in plain English and let AI do the heavy lifting.
At Retoolers, we help teams move faster by combining AI + Retool to create tools that actually fit their workflows.
👉 Check out our blog for the full breakdown: https://lnkd.in/gMAiqy9F
As part of our process, you’ll receive a FREE business analysis to assess your needs, followed by a FREE wireframe to visualize the solution. After that, we’ll provide you with the most accurate pricing and the best solution tailored to your business. Stay tuned—we’ll be in touch shortly!